A cargo vessel may look steady as it sails, but the systems behind its movement are anything but simple. Maritime supply chains connect global vendors, shipyards, and ports that depend on both operational technology and business networks. As CMMC level 2 requirements become a higher bar for compliance, the industry faces hurdles not often visible to outsiders.
Fragmented vendor compliance across global maritime supply chains
International vendors supply critical ship components, but each operates under different rules. This creates inconsistent compliance practices across suppliers, with larger contractors often ahead of smaller vendors. Fragmentation complicates how CMMC compliance requirements are measured, since one weak link can impact the overall certification process.
The challenge multiplies when subcontractors rely on overseas partners. Documentation that may meet local standards does not always align with CMMC level 2 compliance expectations. This lack of alignment forces prime contractors to act as intermediaries, requiring them to pressure smaller suppliers into adopting practices they may not be financially or technically prepared to implement.
Sparse cybersecurity maturity among small shipyard subcontractors
Many small shipyards serve as subcontractors for larger defense contracts. These businesses often have limited budgets and weaker technical infrastructure, which places them closer to CMMC level 1 requirements than advanced frameworks. Their systems may not include multi-factor authentication or security event monitoring—capabilities necessary for higher compliance.
Because defense contracts depend on all tiers of suppliers, these smaller yards become bottlenecks. Without support from consultants such as a CMMC RPO, they risk exclusion from future contracts. The lack of maturity delays progress toward full adoption, putting sensitive maritime defense data at risk.
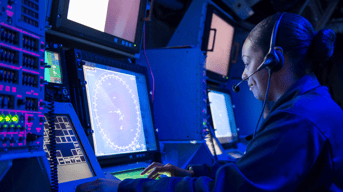
Divergent OT/IT convergence challenges on vessels and terminals
Operational technology, such as navigation and cargo handling systems, operates differently than information technology networks onshore. The convergence of OT and IT introduces vulnerabilities, especially when older vessels rely on legacy control systems. CMMC level 2 requirements emphasize monitoring and access control, yet retrofitting aging OT hardware to meet these standards proves costly.
Ports and terminals also present issues, with multiple systems interacting daily. Cargo scheduling platforms and vessel communications share data, but gaps in integration leave exposures. Balancing cyber defense across both types of networks is difficult because one system demands uptime while the other must prioritize data integrity.
Limited personnel trained in defense-grade control frameworks
Shipyards and terminals often lack staff trained in frameworks that align with CMMC level 2 compliance. Engineers may understand propulsion systems or cargo logistics but not security controls such as audit logging, access policies, or encryption standards. Without trained professionals, compliance plans sit on paper but fail in practice.
The gap grows wider when considering offshore operations, where crews must handle both safety and basic cybersecurity functions. Training programs require investment, yet many organizations delay because they view security as secondary to operations. As compliance deadlines tighten, the absence of skilled personnel will remain a pressing issue.
Inconsistent patching and firmware management in operational systems
Maritime systems often run for years without downtime, making patching cycles irregular. Firmware for navigation devices, engine controllers, or communication terminals may not be updated until vessels are docked for extended maintenance. This delay conflicts with CMMC level 2 requirements that expect timely updates to address vulnerabilities.
Inconsistent patching also occurs in ports, where industrial control systems operate around the clock. Updating these systems often requires halting operations, which companies resist due to financial losses. The result is a backlog of unpatched vulnerabilities that attackers could exploit, highlighting a significant obstacle to compliance.
Inadequate segmentation between navigation and business systems
On many vessels, navigation systems connect to business platforms that manage cargo manifests and crew payroll. Without segmentation, attackers who breach one environment gain access to another. C3PAO auditors will review whether maritime operators enforce strong boundaries, yet achieving this requires redesigned network architecture.
Segmentation adds complexity because vessels often rely on satellite connections that merge multiple services. Ship operators must weigh bandwidth limitations against security requirements, forcing trade-offs that leave exposure points. Until segmentation is treated as mandatory rather than optional, full compliance will remain out of reach.
Complex waiver and equivalency dependencies under Coast Guard rules
The U.S. Coast Guard oversees maritime cybersecurity rules, but waivers and equivalencies add another layer of complexity. Organizations may request exceptions to certain requirements, yet those exceptions must still demonstrate an alternative control with equivalent protection. Aligning these exceptions with CMMC level 2 requirements introduces overlaps that are difficult to reconcile.
Waivers also create inconsistencies between vessels operating under different conditions. A ship granted a waiver may pass one review but fail another when assessed under defense-specific contracts. This uneven landscape places pressure on contractors to interpret multiple sets of rules simultaneously.
Visibility gaps in multi-tier supplier network security postures
Prime contractors often lack full visibility into the security practices of their lower-tier suppliers. Many subcontractors in global maritime supply chains do not disclose security measures, making it hard to verify compliance. This creates blind spots for organizations aiming to meet CMMC level 2 compliance.
The problem intensifies as supply chains stretch across borders. Vendors may self-attest to CMMC compliance requirements but fall short when assessed by a C3PAO. Without improved transparency across supplier networks, higher levels of compliance will remain difficult to achieve.